CAPI Backdoor targets Russia’s auto and e-commerce sectors
A new campaign targets Russia’s auto and e-commerce sectors using a previously unknown .NET malware called CAPI Backdoor.
Cybersecurity researchers at Seqrite Labs uncovered a new campaign, tracked as Operation MotorBeacon, that targeted the Russian automobile and e-commerce sectors with a previously unknown .NET malware dubbed CAPI Backdoor.
“SEQRITE Labs Research Team has recently uncovered a campaign which involves targeting Russian Automobile-Commerce industry which involves commercial as well as automobile oriented transactions , we saw the use of unknown .NET malware which we have dubbed as CAPI Backdoor.” reads the report published by Seqrite Labs.
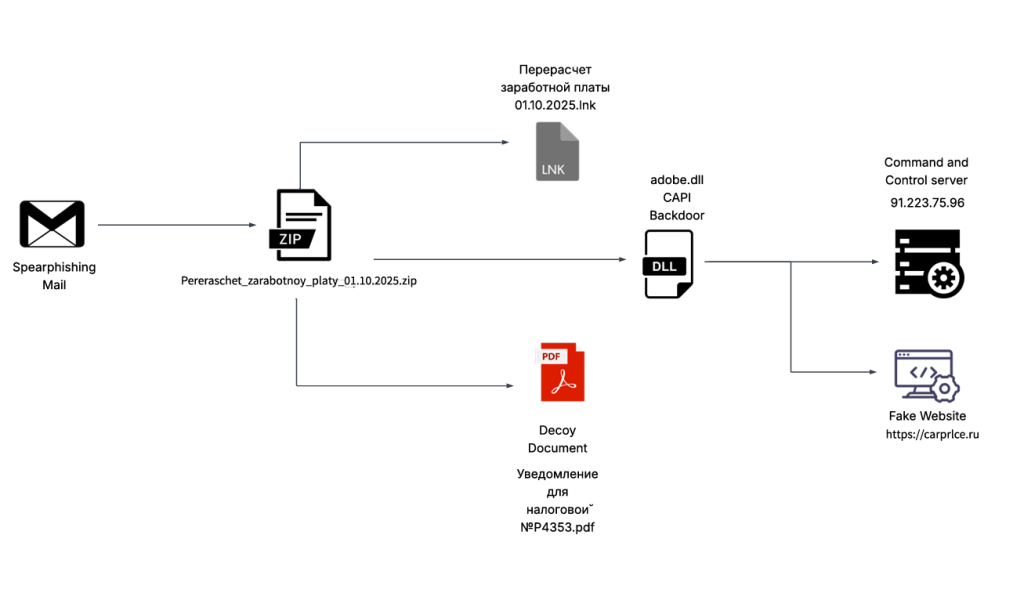
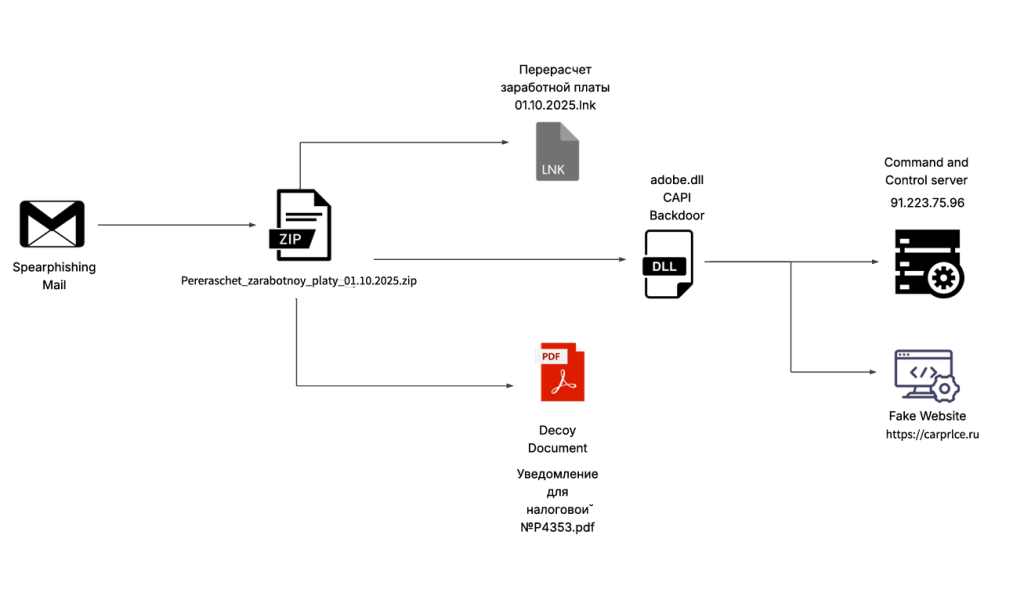
The attack chain starts with phishing emails containing a ZIP archive titled “Перерасчет заработной платы 01.10.2025 (translated Payroll Recalculation as of Oct 1, 2025)” that hides a malicious LNK that runs a .NET implant via rundll32.exe, linking to a C2 server.
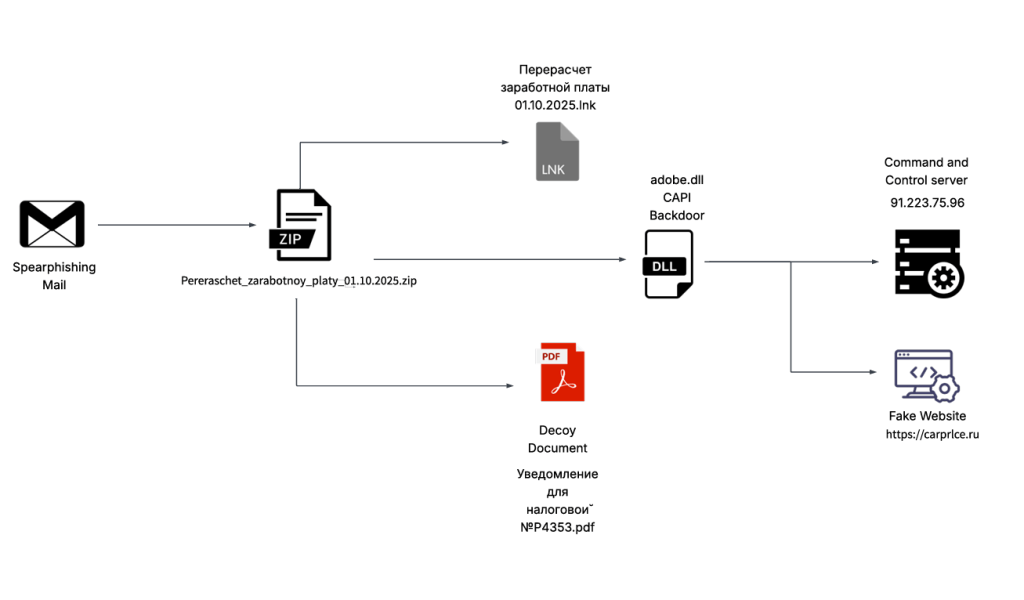
The decoy “Notification for the Tax Office No. P4353.pdf” included in the archive poses as a tax update notice effective Oct 1 2025, detailing a PIT hike from 13% to 15% for incomes > 3 M rubles, showing effects on salaries and urging employees to plan budgets and consult HR.
The LNK file runs a .NET backdoor (“adobe.dll”) via rundll32.exe, checks admin rights and AV tools, then opens the decoy document before connecting to 91.223.75[.]96 to receive commands.
CAPI Backdoor supports multiple functionalities such as stealing browser data (Chrome, Edge, Firefox), taking screenshots, gathering system info, listing folders and exfiltrating results.
The malware runs multiple VM/analysis checks and establishes persistence by creating a scheduled task and placing a LNK in the Windows Startup folder to auto-launch the backdoor DLL from the Roaming directory.
Researchers found two network artifacts tied to the CAPI Backdoor, including a DGA-generated domain. The campaign, active since Oct 3, initially used a fake domain later redirected to a legitimate site. The malware was hosted on port 443 and linked in a spear-phishing lure. Early infrastructure was under ASN 197695 (AS-REG), while data exfiltration occurred via ASN 39087 (P.a.k.t LLC).
“We have been tracking this campaign since October 3rd and discovered that it uses a fake domain, carprlce[.]ru, which closely resembles carprice[.]ru the legitimate domain. This indicates that the threat actor is targeting Russian automobile sector.” concludes the report. “The malicious payload is a .NET DLL that functions as a stealer and establishes persistence for future malicious activities.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Russia)